7 min read
Beyond Buzzwords: Data-Centricity Drives DDS Adoption in the DoD
 Rob Proctor
:
March 18, 2021
Rob Proctor
:
March 18, 2021

Ahh, buzzwords…
Buzzwords pervade all aspects of our life. From politics and social-media to business. Even if you cringe a little whenever someone utters the words “sustainable,” “embedded analytics” or “agile development,” it is important to at least “grok” these terms to understand and communicate with people who use such phrases in non-ironic ways. How else are you going to get to that all-important “synergy”?
No environment is more notorious for buzzwords and phrases than today’s Aerospace and Defense circles. Right now the buzzwords are “swarming” as defense contractors position their respective capabilities for the DoD's planned Combined/Coalition Joint All-Domain Command and Control (CJADC2 or just JADC2) system of systems. The USAF refers to their ABMS program as a new “Internet of Military Things” capability. But what exactly are Multi-Domain Operations, Mosaic Warfare or Joint All Domain Operations anyway?
Keeping buzzwords in mind, in late September of 2020, the U.S. Department of Defense released the long-awaited update to its Data Strategy. It starts with their BLUF (bottom line, up-front. The military’s version of “TL;DR”).
“The DoD Data Strategy supports the National Defense Strategy and Digital Modernization by providing the overarching vision, focus areas, guiding principles, essential capabilities, and goals necessary to transform the Department into a data-centric enterprise. Success cannot be taken for granted...it is the responsibility of all DoD leaders to treat data as a weapon system and manage, secure, and use data for operational effect.”
 In other words, treat data as a strategic asset and share it in a data-centric way. Data-Centricity! What’s that? That might sound buzzword-ish, but here at Real-Time Innovations (RTI), data-centricity is not a hastily-adopted buzzword. Data-centricity is the defining characteristic of our system architecture philosophy for over 15 years.
In other words, treat data as a strategic asset and share it in a data-centric way. Data-Centricity! What’s that? That might sound buzzword-ish, but here at Real-Time Innovations (RTI), data-centricity is not a hastily-adopted buzzword. Data-centricity is the defining characteristic of our system architecture philosophy for over 15 years.
Figure 1 (left): Vision: “DoD is a data-centric organization that uses data at speed and scale for operational advantage and increased efficiency.” 2020 DoD Data Strategy
What Does it Mean to be Data-Centric?
According to Eileen Vidrine, the Air Force's chief data officer (CDO), the new DoD Data Strategy was a collaborative effort between all of the separate DoD CDOs to really focus on data as a strategic asset through data-centricity, “... and that data strategy was really a collaborative effort where the DOD CDO, David Spirk [worked] with the military department CDOs -- Department of Navy, Tom Sasala, David Markowitz, who is the new Army chief data officer, and myself.”
In the DoD Data Strategy, the path to treating data as a strategic asset is with data-centricity. According to Vidrine, “that publication has guiding principles for the entire Department of Defense and it uses the core principles which we call VAULTIS”, which is yet another interesting DoD acronym.
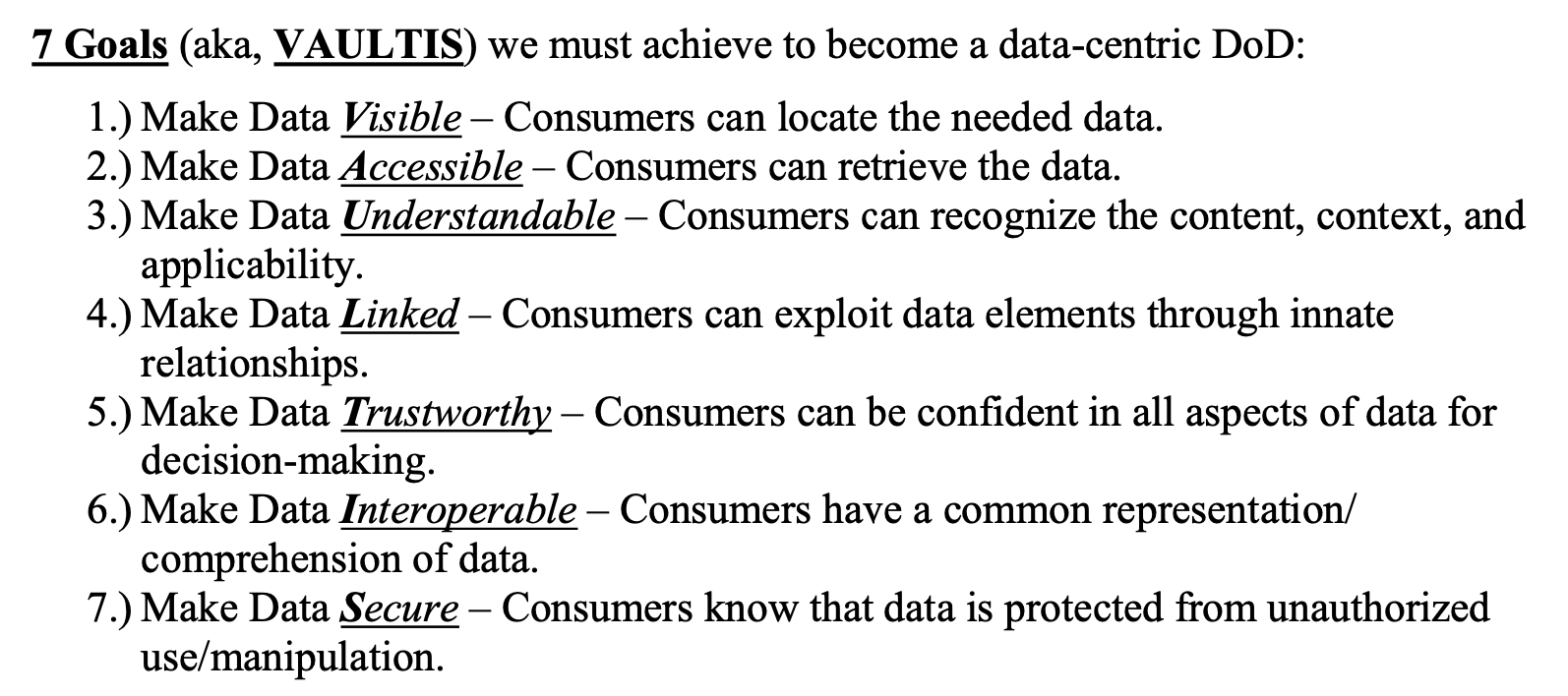
Figure 2 (above): Will “VAULTIS” become a DoD buzzword?
VAULTIS (which sounds more like a Marvel character) is a great list for the characteristics of how to treat data. Only when data is visible, accessible, understandable, linked, trusted, interoperable and secure can warfighters, their commanders and national leaders develop and execute the most effective courses of action. The new Data Strategy is supposed to ensure secure, relevant information exchange across any network between authorized users anytime and anywhere.
The Data Distribution Service™ (DDS) standard has been handling data according to these data-centric practices since its inception in 2004, even adding a comprehensive data-centric security strategy in 2017 to strengthen data integrity.
DDS is Data-Centric
Another way of thinking about data-centricity is that the data itself is the interface between different systems, locations, branches. It is not some messaging protocol that makes you think about who and how to get a data update to several different interested parties. If you are worrying about navigating message brokers, marshalling, serialization or sockets, you are still living in a message-centric way. If there is data to share, it should just be available to those who need it and who have access to it, in the way they each want it. In fact, several different systems might want the same data, but in completely different ways. Data-centricity means that they can get that same data how they need it.
In 2006 RTIs CEO, Stan Schneider, wrote RTI’s first white paper that defined DDS as data-centric. Here is how he described it 15 years ago:
The real change is from code-centric or architecture-centric thinking to data-centric design. Instead of configuring clients and servers, or building data-access objects and invoking remote methods, data-centric design implies that the developer directly controls information exchange. Data-centric developers don’t write or specify code. They build a “data dictionary” that defines who needs what data. Then they answer the information questions: How fast is the data coming? Does it need to be reliable? Do I need to store it? Where is it coming from? What happens if a node fails?
| How it started | How it's going |
|
|
DDS is uniquely data-centric, which ensures that all data includes the contextual information an application needs to understand what data it has to offer and what data it needs to receive. Programmers writing DDS code specify how and when to share data, and then DDS shares the data objects according to those rules. DDS directly implements controlled, managed, and secure data sharing across any peer-to-peer network. It does this by being data aware, which is the real key to being data-centric. DDS knows what the message type is, and when your communications framework knows what the data is, the real data-centric magic can then happen.
So how does this tie back to VAULTIS? I would posit that the goals of making data: Visible, Accessible, Understandable, Linked and Interoperable can all be achieved using RTI Connext® DDS and have been ever since Connext DDS was launched as a product. As part of the DDS discovery process, each participant shares with the other participants what data is visible, accessible and links them. If a radar system joins a network, everybody else discovers what the data model and data topics are for the radar system, and then Connext DDS handles the under the hood interoperability.
The other two characteristics of VAULTIS, Trustworthy and Secure, are tackled through the DDS Security Specification, and by RTI through our Connext DDS Secure product. The DDS Security Technical Specification enables fine-grained, data-centric security in distributed systems. It provides DDS implementations with enhanced security based on data-centric security policies and controls, resulting in the capability to secure systems with the following features:
- Fine-grained control of read and write access, confidentiality, and authentication on a per-topic basis
- Peer-to-peer and serverless authentication capabilities
- Orthogonal data representation, transport, discovery, protocol, and security concerns
- Source-specific data tagging
- Differentiation of read, write and relay permissions
These features allow control over who can access what information and who can control the dissemination of data for each data model topic, as opposed to the entire data stream. These capabilities directly map to the standard security concerns within the global data space for military network systems:
- Authentication: User and device identities can be checked and validated as part of the process of granting access to a domain. Connection to the DDS databus can be separately managed and specified from the connection to the physical layers of the network.
- Access control: Even if connected, users must have specific read and write permissions for a specific topic or an identified set of topics.
- Confidentiality: Discrete data values and related metadata can be encrypted together or separately. Data payloads can be separated and encrypted for confidentiality while routing or implementing last-value historians.
- Integrity: Data samples can include destination-specific signatures or machine access controls (MACs). Integrity can be applied independently or in parallel with confidentiality.
- Availability: Behavior management, fault monitoring and failure actions can be designed into the domain on a per-data-item basis.
DDS Security allows users to secure data-in-motion in mission-critical systems. It is built-in recognition of the fact that different types of data within a system differ in terms of their criticality, and thus should not be treated the same. Thinking of VAULTIS on the whole, the right data-centric security posture means that different security can be chosen for each data topic, from encryption and authentication for highly critical data, to wide open communication for non-sensitive topics. This approach optimizes network and compute bandwidth by encrypting only the most sensitive data, and is further enhanced by Connext DDS Secure’s reliable and secure multicast capabilities.
Why the DoD is “All-in” on Data-Centricity
Most legacy military network systems send information in the form of messages between applications, and programmers who wrote code for those legacy message-centric systems needed to manage the format and context of the messages on both sides of the point-to-point message communication in their application code. It was hard to do then, when there were not as many interoperability requirements. Today, interoperability with anything and everything is the name of the game and using old methods for interoperability is untenable.
“This paradigm shift from a network-centric to a data-centric security model will affect every arena of our cyber domain, focusing first on how to protect our data and critical resources and then secondarily on our networks”
-Vice Admiral Nancy Norton
Director of the Defense Information Systems Agency and Commander of the
Joint Force Headquarters-Department of Defense Information Network
(from a virtual conference in 2020)
The critical factor for using data for joint operations, according to the DoD, will be the coordination between the data governance community and the operational community. Just as a signed governance document does for Connext DDS Secure, the governance community sets principles, policies and other data-related processes to manage data. Then users can use the data to make decisions and launch effects across multiple domains and potentially by multiple branches of the military.
The data strategy states that governance officials need to work closely with the Joint All-Domain Command and Control (JADC2) Cross-Functional Team (CFT), the Joint Artificial Intelligence Center (JAIC), and the Deputy CIO for Command, Control and Communication, “to ensure that we can coordinate information with the tactical edge in a highly contested environment.” David Spirk, DoD’s recently-appointed chief data officer said the strategy was built with the concept of Joint All Domain Command and Control (JADC2) at top of mind, and that the DoD cross-functional team in charge of developing JADC2 has fully adopted the strategy’s goals. “When you lay the data strategy out and you really go to the principles inside of it, it’s about creating operational advantage and efficiencies. The operational advantage puts JADC2 right at the heart of the data strategy, and it was designed to be that way.”
With the new VAULTIS data strategy, it is clear that the DoD has determined that not all of their data is the same and that their systems should not treat all of data the same anymore. Data will underpin digital modernization and is increasingly the fuel of every DoD process, algorithm, and weapon system. “The responsibility of all DoD leaders is to treat data as a weapon system and manage, secure, and use data for operational effect,” Deputy Secretary of Defense David Norquist wrote in the introduction to the strategy. Everyone within the DoD must now treat data as a weapon system and ensure it is made available to others across all domains. The challenge now for the branches is in creating and sharing how to apply data-centric skills and tools to preserve U.S. military advantage.
Your Systems. Working as One.
The DDS standard provides data connectivity, extreme reliability and a scalable communications framework that integrates a wide range of sensor and mission data in a data-centric way. In this manner, DDS covers every characteristic of VAULTIS. DDS is designed from the ground up to meet the necessary interoperability and security requirements for cross-service, cross-supplier and cross-ally integration of a mission-critical, technology-driven operations environment. DDS is ideal for integrating a wide range of disparate network systems, from the smallest sensor to the largest system-of-systems out there, which makes it a low-risk choice for integrating operations and control data for next-generation military network platforms like the CJADC2.
DDS is VAULTIS!
For more information, and to learn more about how Connext DDS can help with C2, ABMS and JADC2, we encourage you to visit with RTI at the NDIA Undersea Warfighter Symposium or contact us at JADC2@rti.com.
About the author
 Rob Proctor is a Lead Field Application Engineer for Real-Time Innovations. He has over 25 years of experience in A&D Embedded Software as a Software Engineer and Field Applications Engineer. Prior to his time as a Field Application Engineer, he developed and implemented real time embedded software at major Aerospace and Defense Corporations. His roles have included developing software and system designs, mission-management and display processing systems. Rob received his BS from Embry-Riddle Aeronautical University in Aerospace Studies and his MS from the University of South Florida in Engineering Management.
Rob Proctor is a Lead Field Application Engineer for Real-Time Innovations. He has over 25 years of experience in A&D Embedded Software as a Software Engineer and Field Applications Engineer. Prior to his time as a Field Application Engineer, he developed and implemented real time embedded software at major Aerospace and Defense Corporations. His roles have included developing software and system designs, mission-management and display processing systems. Rob received his BS from Embry-Riddle Aeronautical University in Aerospace Studies and his MS from the University of South Florida in Engineering Management.
Posts by Tag
- Developers/Engineer (185)
- Technology (81)
- Connext Suite (77)
- News & Events (77)
- Aerospace & Defense (57)
- Standards & Consortia (51)
- Automotive (40)
- IIoT (27)
- 2025 (25)
- Leadership (24)
- Healthcare (23)
- 2024 (22)
- Connectivity Technology (22)
- Cybersecurity (20)
- Culture & Careers (15)
- Military Avionics (15)
- 2026 (14)
- FACE (13)
- ROS 2 (11)
- Connext Pro (10)
- JADC2 (10)
- AI (9)
- Connext Tools (8)
- Connext (7)
- Connext Micro (6)
- Databus (6)
- Transportation (5)
- Case + Code (4)
- Connext Cert (4)
- Energy Systems (4)
- Real-Time Data Streaming (4)
- Robotics (4)
- Golden Dome (3)
- Oil & Gas (3)
- RTI Labs (3)
- Research (3)
- Connext Conference (2)
- Edge Computing (2)
- MDO (2)
- MS&T (2)
- TSN (2)
- ABMS (1)
- DOD (1)
- ISO 26262 (1)
- MOSA (1)
- Simulation (1)
- Teaming (1)
- UAM (1)
- eVTOL (1)
 Success-Plan Services
Success-Plan Services