Vehicle Telematics:
OTA, Teleoperations and Fleet Management
The network starts at the vehicle
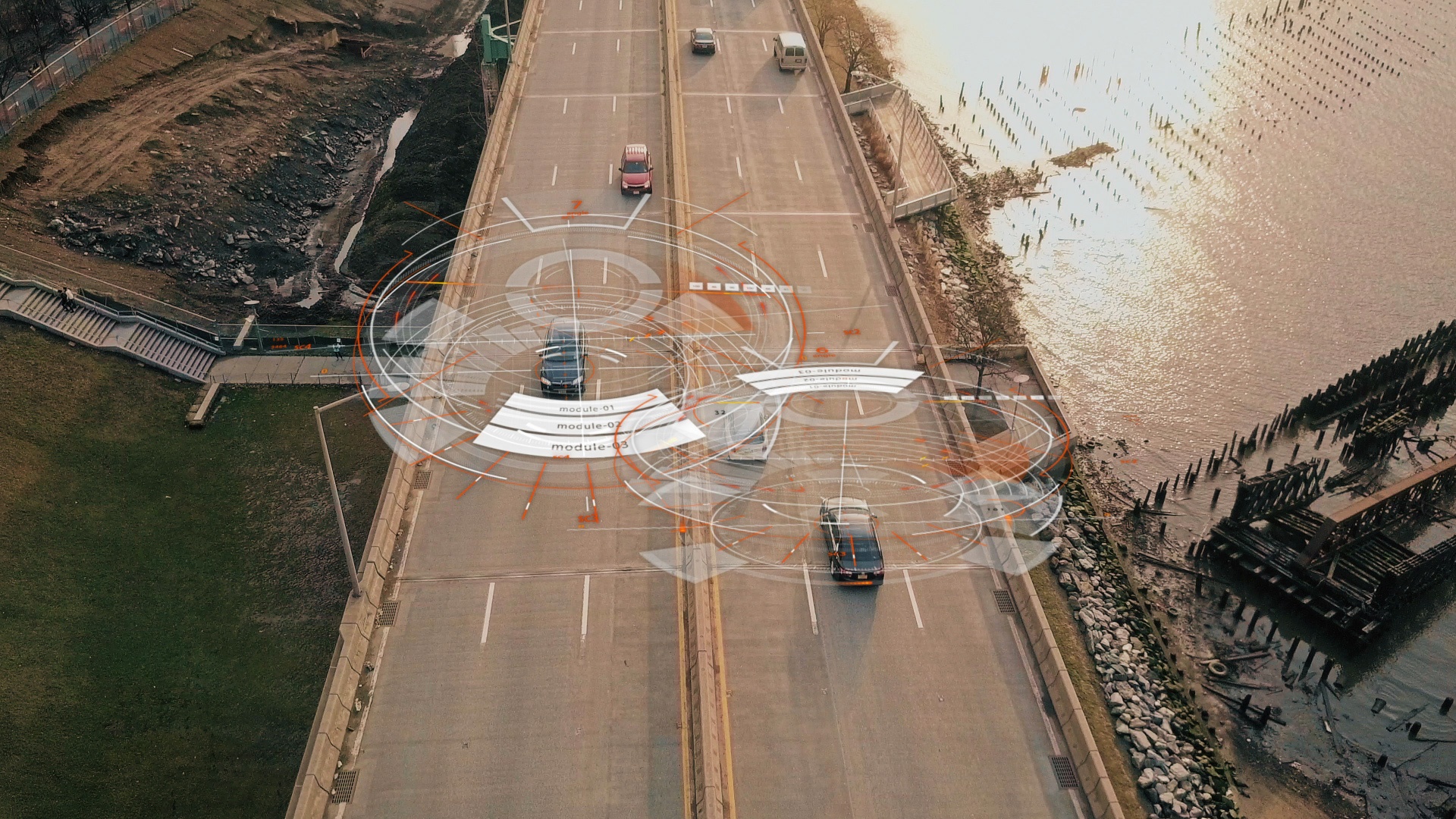
Edge and Cloud-Based Communications
Seamless and efficient data flow from the edge to cloud-based systems
Network-Agnostic,
Real-Time WAN Transport
Cloud Discovery Service
Safety-Critical & Secure Systems
Enabling Modern Telematics Applications
Modern vehicles are increasingly connected and require real-time data flow. As vehicles transition into the software-defined era, the need for continuous, flexible connectivity will be even more important. To be truly competitive, vehicle manufacturers, fleet operators and teleoperations environments require a highly-dynamic and reliable connectivity framework. From over-the-air updates (OTA) to remote vehicle control, the complete supply chain needs to be aligned to overcome major network and vehicle limitations.
Until now, supporting real-time applications in vehicle telematics has been very time-consuming and costly. Unlike systems deployed on local area networks (LANs), many solutions have struggled to adapt to the constraints and complexities of public infrastructure and disruptions caused by roaming and network connectivity. However, given the capabilities enabled by 5G, the automotive industry now increasingly demands reliable, secure and non-intrusive real-time communication, as well as analysis of real-time data and events at high data rates and fidelity, even over unpredictable mobile and wide-area networks.
As vehicles move, critical connectivity must also shift across a diverse set of network infrastructure types – this can translate to a lack of control from the application perspective. Though modern telematics control units provide connectivity leveraging a wide range of technologies such as Wi-Fi, 5G cellular and V2X, the challenges of transitioning between them and handling roaming can easily impact optimum performance.
More detailed information can be found in the Connext Drive Telematics Capability Brief.
 Success-Plan Services
Success-Plan Services
